Download PDF
Download page Monitor Application Security Using Cisco Secure Application.
Monitor Application Security Using Cisco Secure Application
Cisco Secure Application provides a real-time dashboard that provides visibility on the security health of your applications. This dashboard is available when an application is registered with an APM agent and has the appropriate licensing. The agent sends the security events to Cisco Secure Application through the Controller.
The Security Events widget on the AppDynamics Application Dashboard provides high-level information about the security of a registered application. This widget displays the number of critical, warning, and normal security events. To view the details of security for the selected application on Cisco Secure Application, click the Security Events widget.

Select Scope for the Dashboard
Cisco Secure Application dashboard provides a filter to select the required application and tier scope that is applied across all views within this dashboard except Policies. By default, the application scope is the selected application on the AppDynamics dashboard prior to navigating to Cisco Secure Application.
Perform the following to view the data on the dashboard for a specific application:
- Click the filter icon (
 ) <application name/ tier name> on the top right corner of the dashboard.
) <application name/ tier name> on the top right corner of the dashboard. - In the Applications tab, search for the specific application.
- Select the application.
- (Optional) In the Tiers tab, search for the required tier.
If you do not select any specific tier, then data is displayed for all the tiers. - Click Apply Changes.

To return to the default view of all applications, click (![]() <application name/ tier name>) > Applications > Remove App Filter.
<application name/ tier name>) > Applications > Remove App Filter.
Similarly, click (![]() <application name/ tier name>) > Tiers > Remove Tier Filter to return to the default view of all tiers.
<application name/ tier name>) > Tiers > Remove Tier Filter to return to the default view of all tiers.
Navigate to AppDynamics Application or Tier Flowmap
To navigate from the Cisco Secure Application dashboard to the AppDynamics flowmap, click the flowmap icon (![]() ) at the top right corner of the Cisco Secure Application dashboard. The flowmap icon is associated with the selected scope for the Cisco Secure Application dashboard. See Select Scope for the Dashboard.
) at the top right corner of the Cisco Secure Application dashboard. The flowmap icon is associated with the selected scope for the Cisco Secure Application dashboard. See Select Scope for the Dashboard.
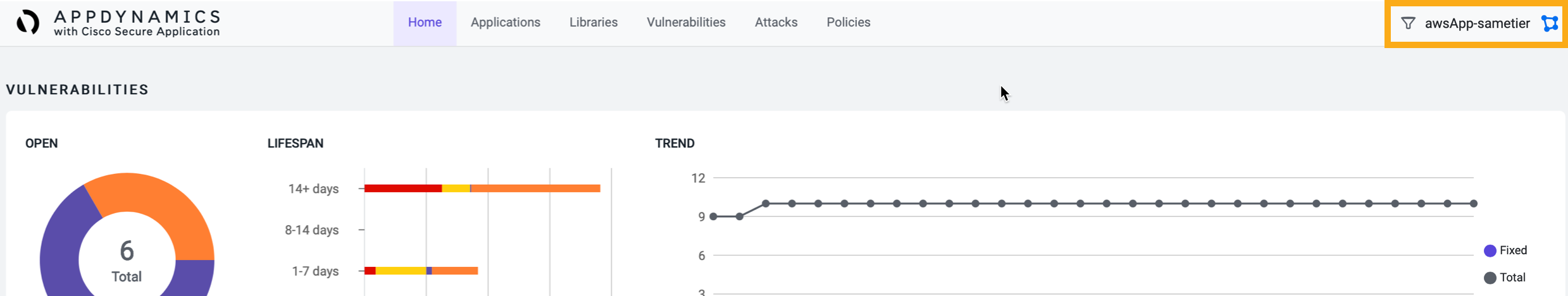
For example, in this image the tier scope is awsApp-sametier1. You can click the flowmap icon (![]() ) to launch the awsApp-sametier1 flowmap on the AppDynamics dashboard.
) to launch the awsApp-sametier1 flowmap on the AppDynamics dashboard.

View Data Using Search Filter
The Cisco Secure Application provides a Search filter on various pages in the dashboard. This filter helps in getting the required data quickly.
The search filter allows you to search based on the selected category.
For example, in the following image these are the categories:
- Vulnerability
- Severity
- Affected Tiers
- Status

You can select the required search category from the dropdown list, then click the Search field to view the list of values corresponding to the category. You can also find the required value as you type.
If you do not require the exact match, you can enter the required generic value in the Search field.
For example, consider that you want to search for all applications that start with a specific prefix, AD. You can select the search category as Application and enter AD in the Search field.
You can search using one or all the categories, but each category can have a single search value. A category is disabled when you specify a search value for that category, but you can continue to select another available category and specify its search value. These search values act as filters. You can remove the search values to remove the search filter.
Cisco Secure Application provides a real-time dashboard that displays these pages:
- Home: This page provides an overall overview of attacks and vulnerabilities of monitored applications.
See Monitor the Home Page of Cisco Secure Application. - Applications: This page provides the details of monitored nodes that are registered with Cisco Secure Application for the managed applications.
See Monitor Security Status of Applications. - Libraries: This page provides details of the existing libraries that require remediation.
See Monitor Libraries. - Vulnerabilities: This page provides information about all discovered vulnerabilities.
See Monitor Vulnerabilities. - Attacks: This page provides information about all detected attacks.
See Monitor Attacks. - Policies: This page allows you to create or customize the policies for vulnerabilities and attacks.
See Cisco Secure Application Policies.